Our Commitment to Information Security
The Advantest Group recognizes the importance of information received from customers and clients, in addition to our company's technology and sales information. We are committed to the proper management of information through the security measures of the Global Information Security Committee, which include establishing regulations, constructing control systems, and providing employee education.
Policies and Rules Related to Information Security
Advantest has established an Information Security Basic Policy. Rules are specified in five policies: our Privacy Policy, Confidential Information Management Policy, Education & Incident Management Policy, IT Security Policy, and Social Media Policy. Each policy will be reviewed by the responsible department, as necessary.
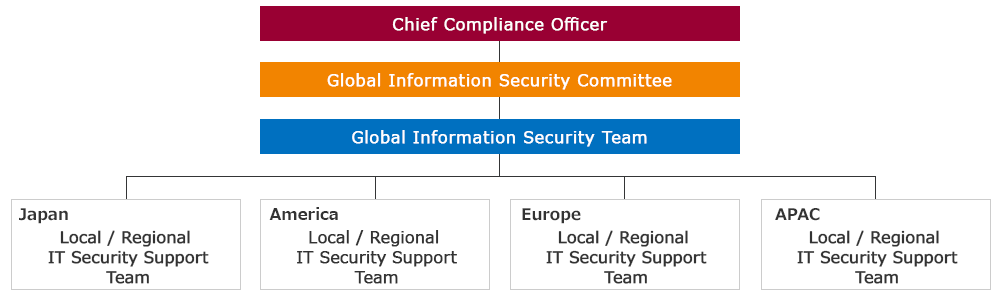
Organization of the Information Security Management System
Advantest acknowledges information security management as a critical business management issue and has instated the Chief Compliance Officer (CCO) as the Information Security Officer within a global system.
Under the CCO are the Global Information Security Committee and Global Information Security Team, with local/regional IT security support teams in each country/region.
The Global Information Security Committee deliberates on information security measures to be applied to the entire Group from various perspectives, and examines the establishment/revision/abolition of policies and rules to be applied to each country/region. Individual security requirements from each country/region are also examined by the Global Information Security Committee and unified responses are taken.
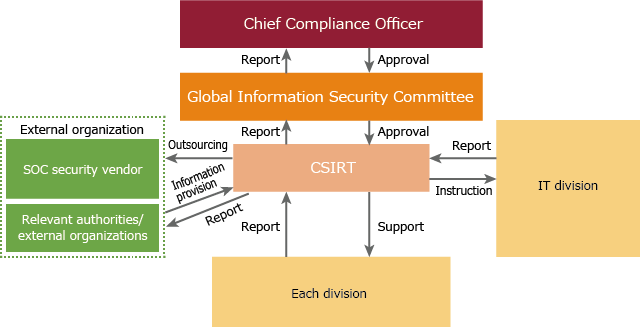
System for Responding to Information Security Incidents
In FY2020, Advantest formed the Advantest CSIRT*1 to reinforce initial response systems for information security incidents. Furthermore, a SOC*2 security monitoring system that operates 24 hours a day, 365 days a year has also been incorporated to facilitate early detection and swift response to global cyberattacks.
Cooperation between related parties in case of damage by a cyberattack is checked once a year. We also determine whether responses to information security incidents are properly functioning by conducting cyberattack training.
If an employee discovers a security incident, the employee will report to the manager immediately. Upon receipt of the report, the manager will contact the IT team of their company or regional headquarters. If the employee cannot reach his/her manager, the employee will contact the nearest IT team.
-
*1CSIRT (Computer Security Incident Response Team)
-
*2SOC (Security Operation Center)
Efforts to protect information
Information Security Training
Based on our belief that people are the last line of defense in information security, our Group is working to ensure that our information security policies and relevant regulations are thoroughly understood. Information security training, in which all employees participate, is based on the policies of "Personal Information Protection", "Confidential Information Management", "Training and Incident Response" and "IT Security" along with training that includes simulations of actual cyberattacks. From FY2021, we changed the information security training platform to provide an environment where employees can take lessons in an easier manner and deepen their understanding.
Furthermore, information on information security is published on the company website to provide information to employees in a timely manner.
Training/Awareness Raising as Part of the Information Security Training
-
Information Security Training through e-learning for all employees: 2
-
Targeted email threat training: 3
-
Broadcast of information to raise awareness: 5
Initiatives for Strengthening Information Security
-
The Advantest Group has established a system in which our audit division conducts information security audits. This enables more objective checks to be carried out based on specified rules and provides a way for the divisions that have been audited to give feedback.
-
Since FY2019, we have been making efforts to further reinforce security by configuring multi-factor authentication in order to prevent identity theft.
-
Security risk assessments and vulnerability tests conducted by external organizations are carried out to objectively evaluate our information security measures, and the results enable us to narrow down the points that need improvement in order to raise our level of security.
-
As security measures, enhanced filtering functions and adding warnings on emails sent from outside the company have been added.
-
Acquired ISO27001 certification to ensure continuous implementation of PDCA to reinforce our level of security. Efforts are underway to achieve certification among the entire Advantest group, including our overseas bases.
Acquisition status of ISO27001 certification
| Country | Registration Date | Scope of Registration |
|---|---|---|
| Japan | August 20, 2021 | Sales, design, development, service, manufacture, and repair of semiconductor and component test systems |
| Germany | July 29, 2022 | Design, development, sales, and service of semiconductor and component test systems |
| U.S.A. | September 28, 2023 | Design, development, sales, and service of semiconductor and component test systems |
| Singapore | August 15, 2024 | Engineering support & service and supply chain management of semiconductor and component test systems |
| Korea | September 1, 2025 | Design, development, and manufacture of semiconductor and component test systems |
| India | September 1, 2025 | Design and development of semiconductor and component test systems |
Confidential Information Protection
Our Information Security Basic Policy defines confidential information as information that has been disclosed by clients under contract along with information that is important to the company. Moreover, the policy stipulates that such information must be handled in accordance with relevant regulations.
Accordingly, we are committed to ensuring that confidential information is not divulged outside the company by ensuring that it is protected through the use of adequate controls governing its storage, disclosure and handling. In fiscal 2024, there were no incidents involving the unauthorized disclosure of important confidential information, etc.
Personal Information Protection
We consider the confidentiality of all personal information entrusted to us to be very important, and accordingly we take steps to ensure that such information is properly protected and managed.
Our commitment to safeguarding personal information entails posting personal information managers in divisions that handle such duties, and ensuring that those managers carry out their duties properly with regard to overseeing such information. Furthermore, we perform regular audits of personal information management and usage practices in each division, and make improvements whenever deficiencies are discovered.
In Group companies outside of Japan, Regional Information Security Officers work to protect and manage personal information in accordance with the laws, regulations, and demands of each respective country or region.
There were no major cases of personal information leaks in FY2024.
IT Security Incident Hotline
To report any IT security related incidents, please contact our 24/7 IT Security Hotline: +1 408-444-9778